Master penetration testing techniques to identify system vulnerabilities and strengthen cybersecurity defenses effectively
Apply ethical hacking tools and methodologies to simulate real-world cyberattacks and assess security risks
Develop comprehensive security assessment reports highlighting vulnerabilities and recommended mitigation strategies
Utilize network scanning and reconnaissance tools to gather critical information for ethical hacking engagements
Implement advanced exploitation techniques to test system defenses without causing damage or disruption
Analyze security breaches to understand attack vectors and improve incident response plans
Design and execute social engineering tests to evaluate organizational security awareness and employee training needs
Stay updated with the latest cybersecurity threats, hacking tools, and ethical hacking best practices
Configure and manage firewalls, intrusion detection systems, and security protocols to prevent unauthorized access
Conduct vulnerability assessments and prioritize remediation efforts based on risk levels
Understand legal and ethical considerations in ethical hacking to ensure compliance and responsible testing
Collaborate with cybersecurity teams to develop proactive security strategies and enhance overall organizational security
Course Content
المحتوى
-
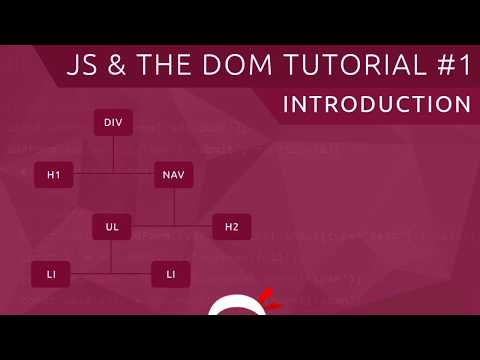
Ethical Hacking In 8 Minutes | What Is Ethical Hacking | Ethical Hacking Explanation | Simplilearn
00:00 -
Ethical Hacking In 2 Minutes | What Is Ethical Hacking | Ethical Hacking Explained | Simplilearn
00:00 -
What Is Ethical Hacking | Ethical Hacking Tutorial For Beginners | Ethical Hacking | Simplilearn
00:00 -
Ethical Hacking Full Course In 3 Hours| Learn Ethical Hacking| Ethical Hacking Tutorial|Simplilearn
00:00 -
Best Programming Languages For Hacking | Important Languages For Hacking | Simplilearn
00:00 -
Ethical Hacking And Penetration Testing Guide | Ethical Hacking Tutorial For Beginners | Simplilearn
00:00 -
Ethical Hacking Penetration Testing | Penetration Testing Tutorial | Cyber Security | Simplilearn
00:00 -
SQL Injection Tutorial For Beginners | What Is SQL Injection | Cyber Security Course | Simplilearn
00:00 -
CEH Course | Certified Ethical Hacker Certification | Ethical Hacking Course | Simplilearn
00:00 -
Certified Ethical Hacker Certification | Certified Ethical Hacker Course | CEH | Simplilearn
00:00 -
CEH V11 Certification | How To Get CEH V11 Certification | CEH V11 Exam Details | Simplilearn
00:00 -
Certified Ethical Hacker V10 Tutorial | CEH V10 Tutorial | CEH V10 Training Video | CEH |Simplilearn
00:00 -
CEH Exam | Certified Ethical Hacker Exam | CEH Certification Exam | CEH Exam Tips | Simplilearn
00:00 -
How To Become A Certified Ethical Hacker | Ethical Hacker Career Path | Ethical Hacking |Simplilearn
00:00 -
Top Ethical Hacking Certifications | Certified Ethical Hacker | Ethical Hacking Training|Simplilearn
00:00 -
Best Books To Learn Ethical Hacking For Beginners | Learn Ethical Hacking 2021 | Simplilearn
00:00 -
Ethical Hacking Career Skills Salary And Resume | How To Become An Ethical Hacker | Simplilearn
00:00 -
Ethical Hacking Career 2021 | Ethical Hacking Jobs Scope Salary | Ethical Hacking | Simplilearn
00:00 -
Top 10 Most Dangerous Hackers Of All Time | Top 10 Hackers In The World | Simplilearn
00:00 -
Top Cyber Attacks In History | Biggest Cyber Attacks Of All Time | Cyber Security | Simplilearn
00:00 -
Ethical Hacking Interview Questions Answers | Ethical Hacking Interview Preparation | Simplilearn
00:00 -
What Is Kali Linux | What Is Kali Linux And How To Use It | Kali Linux Tutorial | Simplilearn
00:00 -
Kali Linux Tutorial 2021 | Kali Linux For Beginners | Learn Kali Linux | Ethical Hacking|Simplilearn
00:00 -
Parrot Security OS Installation Tutorial 2021 | How To Install Parrot OS In Virtualbox | Simplilearn
00:00 -
What Is Parrot Security OS | Introduction To Parrot Security OS | Cyber Security | Simplilearn
00:00 -
What Is Wireshark | What Is Wireshark And How It Works | Wireshark Tutorial 2021 | Simplilearn
00:00 -
How To Detect Keylogger On Computer | Keylogger Detection Removal | Ethical Hacking | Simplilearn
00:00 -
Kali Linux vs Parrot OS Which Is Best For Hacking | Best Hacking Operating System |Simplilearn
00:00 -
Kali Linux For Ethical Hacking | Kali Linux For Beginners 2021 | Ethical Hacking | Simplilearn
00:00 -
Ethical Hacking Career 2022 Salary Scope Jobs Skills | Ethical Hacking RoadMap | Simplilearn
00:00 -
Penetration Testing | Penetration Testing For Beginners | Penetration Testing Tools | Simplilearn
00:00 -
How To Become Ethical Hacker In 2022 | Ethical Hacker Roadmap 2022 | Ethical Hacker | Simplilearn
00:00 -
Nmap Tutorial For Beginners | Nmap Vulnerability Scan Tutorial | Nmap Hacking Tutorial | Simplilearn
00:00 -
Ethical Hacking Using Python | Python Ethical Hacking Tutorial | Ethical Hacking | Simplilearn
00:00 -
Nmap Tutorial For Beginners | How To Scan Your Network Using Nmap | Ethical Hacking | Simplilearn
00:00 -
Metasploit For Beginners | What is Metasploit Explained | Metasploit Basics Tutorial | Simplilearn
00:00 -
Final Exam – Ethical Hacking
A course by
Student Ratings & Reviews